Parent process spoofing and how to detect them
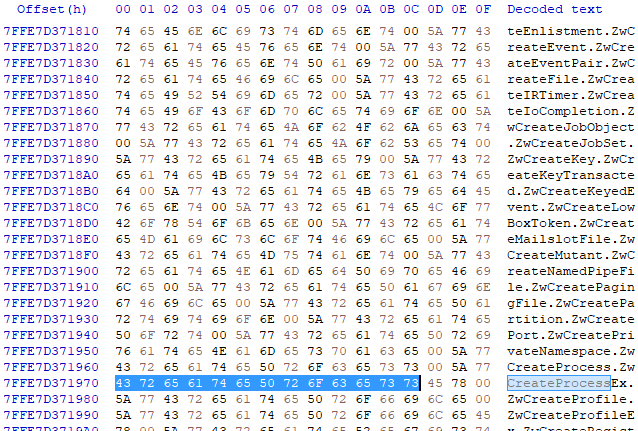
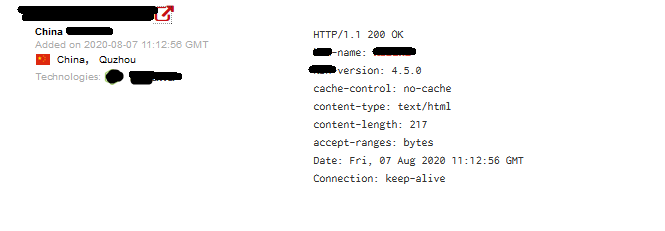
Malware uses vaious techniques to hide it or evade from antivirus or EDR system. So I decided to discuss about a very intresting malware hiding technique Parent process spoofing. This technique is well discussed by many other infosec people and Didier Stevens blogged about this in 2009. I decided to discuss in layman form. parent process spoofing technique allows a malicious program to spawn a process of its choice. It helps the malicious program to hide itself from the parent-child process analyzing which helps defender to find anomalies. How Does It work This is an abuse of windows feature It uses a Windows API CreatProcessA function which use to create a new process. This function has a parameter lpStartupinfo which allows you to choose the parent process. lpStartupinfo points to STARTUPINFOEX structure The STARTUPINFOEX structure contains lpAttributeList lpAttributelist is created by InitializeProcThreadAttributeList function...